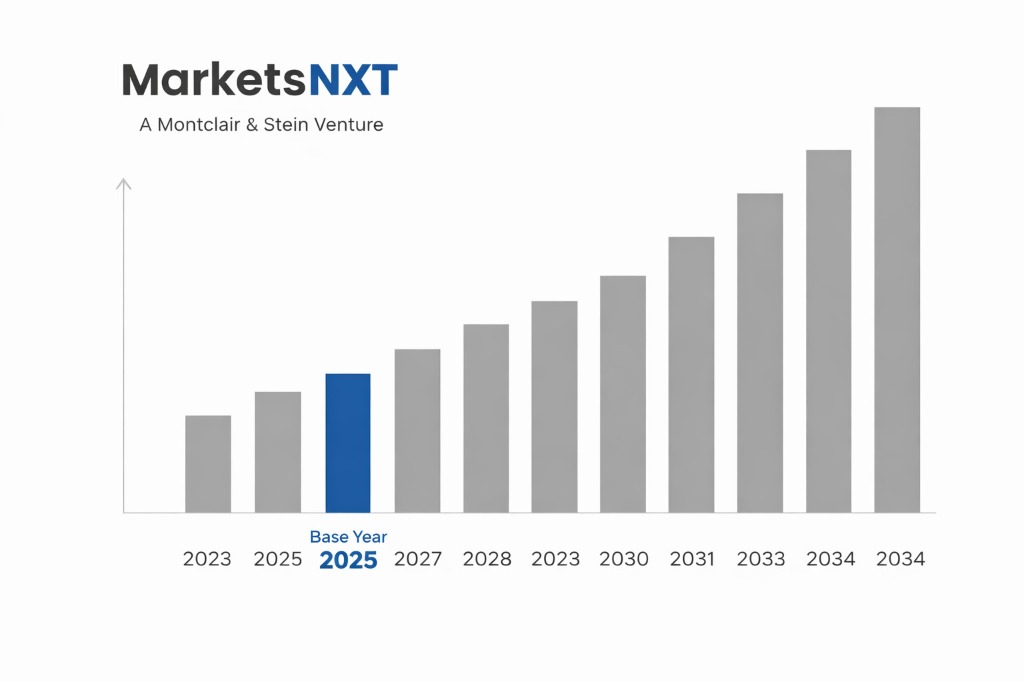
AI-Powered Cybersecurity Market Size, Share & Forecast 2026–2034
Report Highlights
- ✓Market Size 2024: USD 20.2 billion
- ✓Market Size 2034: USD 121.3 billion
- ✓CAGR: 21.0%
- ✓Market Definition: AI and machine learning platforms for threat detection, SOC automation, identity security, and cyber risk management.
- ✓Leading Companies: CrowdStrike, Palo Alto Networks, Microsoft Security, SentinelOne, Darktrace
- ✓Base Year: 2025
- ✓Forecast Period: 2026–2034
Who Controls This Market — And Who Is Threatening That Control
CrowdStrike's Falcon platform processes more than 1 trillion security events daily from approximately 24,000+ enterprise customers, creating the largest real-time threat intelligence feedback loop in commercial cybersecurity. Charlotte AI — CrowdStrike's generative AI SOC analyst — can query the Threat Graph in natural language, correlate incidents across the entire customer base, and generate investigation summaries that reduce mean time to respond from hours to minutes. CrowdStrike's competitive advantage is data density: each new customer's telemetry improves detection accuracy for all other customers simultaneously — a data network effect that compounds every year and is impossible for a new entrant to replicate without a comparable installed base.
Microsoft Security has grown from a marginal player to the world's largest cybersecurity revenue generator (USD 20+ billion annually across its security product portfolio) by leveraging its identity (Azure Active Directory), endpoint (Defender), and cloud infrastructure positions to create an integrated security data lake that no standalone cybersecurity company can match. Microsoft's Security Copilot — built on GPT-4 — can correlate identity signals, endpoint behaviour, email threats, and cloud activity across the Microsoft ecosystem in natural language queries, with context spanning the entire Microsoft tenant's security history. Microsoft's advantage is cross-product data integration; its limitation is that non-Microsoft environments require additional agent deployment, weakening the correlation advantage in heterogeneous enterprise IT environments.
Palo Alto Networks' Cortex XSIAM (AI-driven SOC platform) and Precision AI framework represent the most architecturally coherent AI-native security operations platform from a traditional security vendor, combining network, endpoint, cloud, and identity telemetry into a unified AI analysis layer. Palo Alto's 'platformisation' strategy — offering extended free trials and pricing incentives for customers to replace point solutions with integrated Cortex capabilities — is compressing revenue for standalone SIEM (Splunk), SOAR, and EDR vendors in accounts where Palo Alto has network security installed, demonstrating the consolidation dynamic at scale.
Industry Snapshot
The global AI-powered cybersecurity market generated approximately USD 22.4 billion in 2024, representing approximately 15%–18% of total cybersecurity spending. AI integration in cybersecurity products is moving from a differentiating feature to a baseline expectation: every major SIEM, EDR, and XDR product now includes at least one AI-powered detection or investigation feature, making the boundary between 'AI cybersecurity' and 'conventional cybersecurity' increasingly blurred. The fastest-growing AI cybersecurity segment is generative AI for SOC automation — natural language interfaces for security investigation, automated playbook generation, and AI-assisted threat hunting — growing at estimated 65%–80% annually in 2024.
The threat landscape is simultaneously the primary demand driver and the primary source of AI cybersecurity market complexity. AI-generated phishing emails — indistinguishable from legitimate communications in grammar, tone, and contextual accuracy — have increased business email compromise (BEC) attack success rates by estimated 40%–60% in 2023–2024. AI-assisted vulnerability exploitation tools have compressed the median time from public CVE disclosure to first exploit attempt from 14 days in 2021 to less than 24 hours in 2024. Nation-state threat actors (Volt Typhoon, Cozy Bear, Lazarus Group) are integrating AI-assisted reconnaissance, malware polymorphism, and living-off-the-land technique variation into multi-stage attack campaigns that evade signature-based detection with increasing reliability.
The Forces Accelerating Demand Right Now
The asymmetric risk of AI-assisted attacks is forcing enterprise security teams to adopt AI-powered defences regardless of budget constraints. An attacker using LLM-generated spear phishing customised to each recipient's professional background and communication style can achieve 35%–45% click rates versus 5%–10% for generic phishing, according to security awareness training programme data. AI-generated malware variants that modify their own code signatures on each execution defeat hash-based endpoint detection that was the enterprise security standard for 30 years. The operational implication: signature-based security products that do not incorporate behavioural AI detection are becoming structurally inadequate, creating a forced upgrade cycle across the entire enterprise security product portfolio.
The largest single labour cost in enterprise cybersecurity is the Security Operations Centre — a 24/7 operation staffing 5–100 analysts per enterprise depending on size, at USD 80,000–150,000 per analyst annually. Tier-1 SOC functions (alert triage, initial investigation, false positive filtering) account for 60%–70% of analyst time and are highly automatable by AI agents that can query SIEM data, correlate alerts, investigate indicators of compromise, and generate investigation summaries in seconds. CrowdStrike's Charlotte AI, Palo Alto's Cortex XSIAM, and purpose-built AI SOC platforms (Dropzone AI, Torq) are claiming 80%–95% reduction in tier-1 analyst workload — a USD 15–25 billion annual SOC labour cost automation opportunity that is the largest single AI efficiency play in the enterprise software market.
What Is Holding This Market Back
When an AI-powered security system autonomously blocks a user's account, isolates a server, or terminates a network connection based on anomaly detection, it makes a decision with operational impact without human review. Financial services regulators (OCC, ECB banking supervision), healthcare regulators (HHS OCR), and critical infrastructure operators (NERC CIP) require that automated security actions be explainable, auditable, and subject to human override. The EU AI Act classifies AI systems used in critical infrastructure security as 'high risk,' requiring documentation, human oversight, and conformity assessment — regulatory requirements that limit the degree to which AI security systems can operate fully autonomously in regulated industries. This tension between security effectiveness (speed requires automation) and regulatory compliance (accountability requires human oversight) is the primary constraint on AI SOC automation deployment in regulated verticals.
AI-powered anomaly detection systems that learn 'normal' behavioural baselines are subject to alert fatigue — the production of large numbers of low-confidence anomaly alerts that analysts must manually review and dismiss. CrowdStrike's own post-incident analysis of its July 2024 Falcon sensor update (which crashed 8.5 million Windows devices globally) demonstrated the operational risk of over-relying on automated security system changes without adequate testing stages. Security teams that have experienced AI false positive floods — particularly in initial post-deployment periods before models are tuned — develop institutional resistance to AI automation that slows additional deployment and undermines the vendor relationship.
The Investment Case: Bull, Bear, and What Decides It
The bull case is AI SOC platforms achieving 90%+ automation of tier-1 analyst functions with false positive rates below 0.5% by 2027, making enterprise-grade 24/7 SOC economics viable for the 95%+ of organisations with fewer than 100 IT staff that currently cannot staff a SOC. Under this scenario, the mid-market security segment (100–5,000 employees) transitions from 'essentially unprotected' to 'AI-SOC protected' at USD 50,000–200,000 per year, creating a USD 50+ billion addressable market expansion that existing cybersecurity vendors have not penetrated. Bull case probability: 35%.
The bear case is AI-powered attack tools achieving offensive parity with AI-powered defences — attackers using AI to generate novel, never-seen-before attack techniques faster than defensive AI models can be trained on new threat data. In this scenario, overall breach rates do not decline despite AI cybersecurity investment, undermining the ROI case, CFO confidence in cybersecurity AI spending declines, and market growth slows to 12%–15% CAGR as buyers become more selective. Security insurance premiums continue rising, and regulation shifts toward liability assignment rather than technical security investment. Bear case probability: 20%.
The decisive indicators are published AI SOC false positive rates and breach rate data from the Verizon Data Breach Investigations Report and IBM Cost of a Data Breach Report for 2025 and 2026. If organisations with AI-powered security show statistically significant reductions in breach rates and dwell times versus those without, capital allocation to AI cybersecurity increases across all enterprise segments. If breach rates are unchanged despite AI investment, budget scrutiny increases. The CrowdStrike July 2024 incident's impact on enterprise AI automation confidence is a near-term sentiment headwind to monitor.
Where the Next USD Billion Is Being Built
The 3–5 year opportunity is AI-powered OT (operational technology) security for industrial control systems, utilities, and critical infrastructure. Traditional OT security was passive monitoring — OT networks cannot be patched on the same schedule as IT networks due to availability requirements — but AI-powered anomaly detection for SCADA, DCS, and ICS systems can detect lateral movement, command injection, and protocol anomaly without requiring patching or active intervention. Dragos, Claroty, and Nozomi Networks are the current OT security leaders, but CrowdStrike's extension of Falcon into OT environments and Palo Alto's acquisition of Claroty (rumoured) signal that horizontal platform players see OT as the next consolidation frontier. The 18,000+ US critical infrastructure operators with inadequate OT security represent a USD 5–8 billion near-term addressable market.
The 5–10 year opportunity is AI security for AI systems — protecting large language models, multimodal AI systems, and AI agents from adversarial attacks, data poisoning, model extraction, and prompt injection. As enterprises deploy AI in revenue-generating and decision-critical applications, the AI system itself becomes an attack surface: prompt injection attacks that manipulate AI agent behaviour, model inversion attacks that extract proprietary training data, and adversarial examples that fool AI vision systems are attack vectors with no equivalent in traditional cybersecurity frameworks. The AI red-teaming, LLM security monitoring, and adversarial robustness testing market is nascent (HiddenLayer, Robust Intelligence, Adversa AI are early examples) but will scale to USD 5–10 billion as AI application deployment proliferates.
Market at a Glance
| Parameter | Details |
|---|---|
| Market Size 2024 | USD 20.2 billion |
| Market Size 2034 | USD 121.3 billion |
| Growth Rate | 21.0% CAGR (2026–2034) |
| Most Critical Decision Factor | Technology maturity and enterprise deployment readiness |
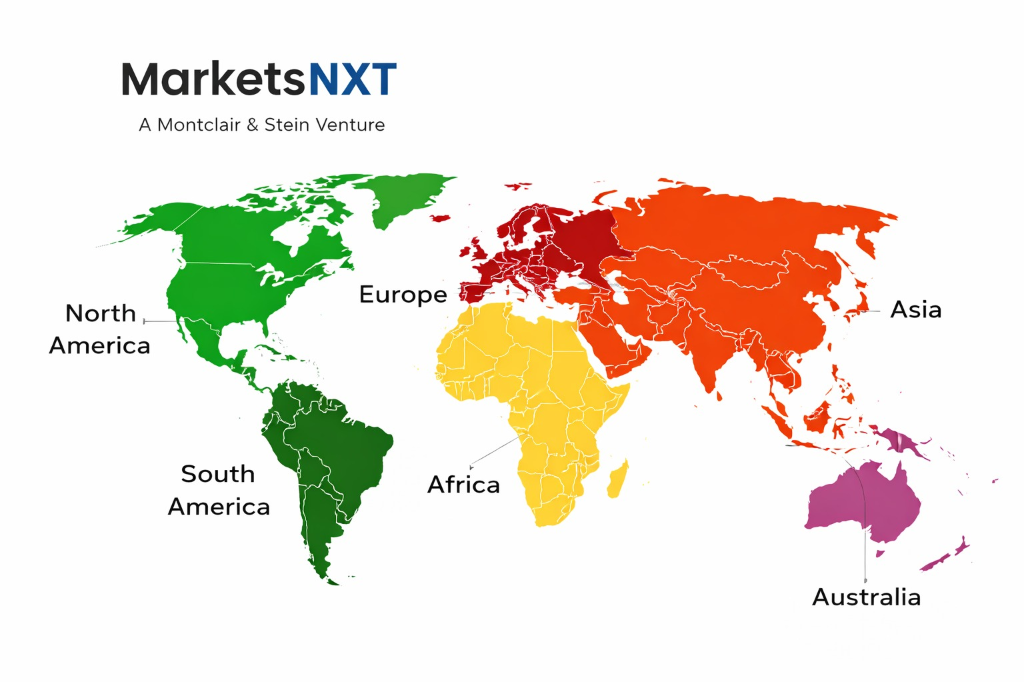
| Largest Region | North America |
| Competitive Structure | High — platform consolidation compressing point solution economics, data |
Regional Intelligence
The NIS2 Directive (EU, effective October 2024) significantly expands cybersecurity obligations across 18 critical sectors including energy, transport, health, banking, digital infrastructure, and public administration — requiring risk management measures, incident reporting within 24 hours of awareness, and management accountability for cybersecurity compliance. NIS2 covers approximately 160,000 entities across the EU (versus approximately 5,000 under NIS1), creating a large new compliance-driven demand for AI-powered security monitoring and incident response capability. The EU's Cyber Resilience Act (agreed 2024) establishes cybersecurity requirements for products with digital elements — IoT devices, industrial control systems, consumer electronics — creating product security obligations for manufacturers that drive AI-powered secure development lifecycle tooling.
The US SEC's cybersecurity disclosure rules (effective December 2023) require public companies to disclose material cybersecurity incidents within 4 business days of determining materiality, and annually disclose cybersecurity governance, risk management, and strategy. The disclosure requirement creates board-level accountability for cybersecurity programmes that drives investment in AI-powered security operations capable of detecting and characterising incidents within the SEC's materiality determination timeline — a compliance driver that affects all 4,000+ US public companies. The CISA's Cyber Performance Goals (CPGs) provide a voluntary baseline for critical infrastructure security that is increasingly referenced in federal contracting requirements.
Leading Market Participants
- CrowdStrike
- Palo Alto Networks
- Microsoft Security
- SentinelOne
- Darktrace
- Vectra AI
- Exabeam
- Securonix
- Google Cloud Security
- IBM Security
Long-Term Market Perspective
By 2034, AI will be the foundational layer of cybersecurity operations — not a feature but the architecture. The cybersecurity workforce will have restructured: tier-1 and tier-2 SOC analyst roles will be largely automated, with human analysts specialising in adversarial AI research, incident strategy, regulatory liaison, and governance functions that require contextual judgment AI cannot provide. Cybersecurity spending will increase in absolute terms (driven by threat escalation and regulatory expansion) but the efficiency gain from AI automation will allow organisations to achieve higher security posture with a smaller headcount than 2024 levels — a productivity gain analogous to the ERP automation of manual accounting functions in the 1990s.
The most consequential long-term development is the emergence of AI-to-AI adversarial dynamics at nation-state scale — fully autonomous offensive AI agents conducting reconnaissance, exploitation, and persistence establishment against target networks without human direction, countered by autonomous defensive AI agents operating at machine speed. The Geneva Conventions have no framework for autonomous AI cyberwarfare; NATO's Tallinn Manual 3.0 process is beginning to address it; regulatory frameworks are not. The outcome of early AI-to-AI cyber engagements in state-sponsored conflicts will determine both the technical direction of AI security development and the geopolitical pressure for international AI cyberwarfare norms.
Frequently Asked Questions
Market Segmentation
- Endpoint Detection and Response
- Security Information and Event Management
- Network Traffic Analysis and Intrusion Detection
- Identity and Access Management Anomaly Detection
- Cloud Security Posture Management
- AI-Powered Threat Intelligence and Dark Web Monitoring
- Cloud-Native SaaS Security Platform
- On-Premise or Private Cloud
- Hybrid Managed Detection and Response
- AI SOC-as-a-Service
- Financial Services and Banking
- Healthcare and Life Sciences
- Government and Defence
- Retail and E-Commerce
- Industrial and Critical Infrastructure
Table of Contents
Research Framework and Methodological Approach
Information
Procurement
Information
Analysis
Market Formulation
& Validation
Overview of Our Research Process
MarketsNXT follows a structured, multi-stage research framework designed to ensure accuracy, reliability, and strategic relevance of every published study. Our methodology integrates globally accepted research standards with industry best practices in data collection, modeling, verification, and insight generation.
1. Data Acquisition Strategy
Robust data collection is the foundation of our analytical process. MarketsNXT employs a layered sourcing model.
- Company annual reports & SEC filings
- Industry association publications
- Technical journals & white papers
- Government databases (World Bank, OECD)
- Paid commercial databases
- KOL Interviews (CEOs, Marketing Heads)
- Surveys with industry participants
- Distributor & supplier discussions
- End-user feedback loops
- Questionnaires for gap analysis
Analytical Modeling and Insight Development
After collection, datasets are processed and interpreted using multiple analytical techniques to identify baseline market values, demand patterns, growth drivers, constraints, and opportunity clusters.
2. Market Estimation Techniques
MarketsNXT applies multiple estimation pathways to strengthen forecast accuracy.
Bottom-up Approach
Aggregating granular demand data from country level to derive global figures.
Top-down Approach
Breaking down the parent industry market to identify the target serviceable market.
Supply Chain Anchored Forecasting
MarketsNXT integrates value chain intelligence into its forecasting structure to ensure commercial realism and operational alignment.
Supply-Side Evaluation
Revenue and capacity estimates are developed through company financial reviews, product portfolio mapping, benchmarking of competitive positioning, and commercialization tracking.
3. Market Engineering & Validation
Market engineering involves the triangulation of data from multiple sources to minimize errors.
Extensive gathering of raw data.
Statistical regression & trend analysis.
Cross-verification with experts.
Publication of market study.
Client-Centric Research Delivery
MarketsNXT positions research delivery as a collaborative engagement rather than a static information transfer. Analysts work with clients to clarify objectives, interpret findings, and connect insights to strategic decisions.