Next-Generation Firewall Market Size, Share & Forecast 2026–2034
Report Highlights
- ✓Market Size 2024: Approximately USD 6.2 billion
- ✓Market Size 2034: Approximately USD 18.8 billion
- ✓CAGR Range: 11.8%–14.2%
- ✓Market Definition: Next-generation firewalls (NGFW) are network security platforms integrating deep packet inspection, application-layer visibility, intrusion prevention, SSL inspection, and identity-based policy enforcement — moving beyond port/protocol filtering to application-aware and user-aware traffic control across hybrid cloud and on-premise environments
- ✓Top 3 Competitive Dynamics: Palo Alto Networks' AI-driven platform consolidation strategy pressuring point-solution NGFW vendors; Fortinet's price-performance advantage via custom ASIC accelerators creating a mid-market dominance that cloud-native challengers cannot match on total cost of ownership; the migration to SASE (Secure Access Service Edge) architecturing NGFW functions natively into cloud-delivered security creating structural displacement risk for hardware-dependent incumbents
- ✓First 5 Companies: Palo Alto Networks, Fortinet, Cisco, Check Point Software, Juniper Networks
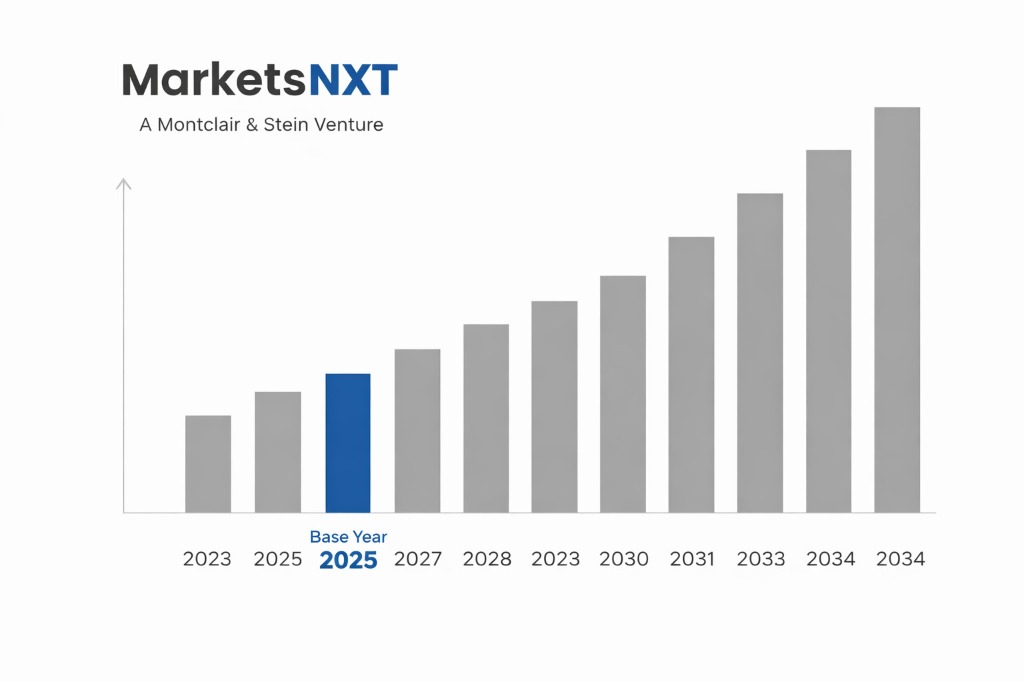
- ✓Base Year: 2025
- ✓Forecast Period: 2026–2034
- ✓Contrarian Insight: The NGFW market's headline growth understates the category disruption underway — traditional hardware NGFW is declining in enterprise data centres while cloud-delivered NGFW and SASE are growing at 25%–35% annually; the market is not expanding uniformly but bifurcating between a commoditising hardware segment and a premium cloud-delivered security platform segment with very different competitive dynamics
Who Controls This Market — And Who Is Threatening That Control
Palo Alto Networks holds the most strategically positioned competitive stance — not by market share alone (approximately 20%–24% of NGFW revenue) but by the completeness of its platform consolidation strategy. Its Strata Network Security platform integrates NGFW, SASE, and AI-driven Security Operations Centre capabilities under a unified management console, directly addressing the enterprise pain point of security tool proliferation. Palo Alto's platformisation revenue strategy — offering discounts for customers adopting three or more platform products — is compressing margins today but building switching costs that will compound through 2030. Fortinet commands the largest installed base globally by unit volume, built on the price-performance advantage of its proprietary FortiASIC network processors that deliver hardware-accelerated NGFW performance at 30%–40% lower total cost of ownership than software-based alternatives — a moat that is structurally defended as long as on-premise network infrastructure remains a significant deployment model.
The structural threat to both is Zscaler, Netskope, and Cloudflare's SASE platforms — architectures that deliver NGFW functionality natively in cloud, eliminating the need for hardware appliances at branch offices and enterprise data centre perimeters. SASE adoption is still predominantly additive (companies running SASE alongside legacy NGFW during transition), but the 5–7 year trajectory points toward SASE as the primary security architecture for distributed enterprise, gradually eroding the renewal cycle that sustains hardware NGFW incumbents.
Three competitive moves will determine leadership through 2028: which vendor achieves the most credible AI-native threat detection capability that reduces security analyst workload by measurable percentages; which NGFW platform builds the most productive MSSP (managed security service provider) channel for mid-market customers who cannot support in-house security operations; and which company most effectively bridges the hardware-to-cloud transition for its installed base without cannibalising hardware renewal revenue.
Industry Snapshot
The Next-Generation Firewall market was valued at approximately USD 6.2 billion in 2024 and is projected to reach approximately USD 18.8 billion by 2034, growing at a CAGR of 11.8%–14.2% over the forecast period. The market is in a structural architecture transition — from hardware-appliance-dominant to cloud-delivered and hybrid deployment models — that is creating simultaneous growth in cloud NGFW and decline in traditional hardware NGFW in enterprise data centres. Total market growth reflects the net of these opposing vectors plus the expansion of NGFW deployment to previously unprotected environments: OT networks, IoT device segmentation, and cloud workload protection. The compliance driver is a consistent demand floor — PCI DSS 4.0, HIPAA, NIS2 Directive, and SEC cybersecurity disclosure rules all create non-discretionary NGFW investment requirements for regulated industries.
The value chain spans NGFW hardware and OS development, cloud-delivered NGFW service operation, threat intelligence feeds (Palo Alto Unit 42, Fortinet FortiGuard, Check Point ThreatCloud), management and analytics platforms, and professional services for implementation and managed detection and response. The intelligence and analytics layer is becoming the primary competitive differentiator as hardware performance increasingly commoditises — vendors that process the most threat telemetry improve detection accuracy in a virtuous cycle that smaller competitors cannot replicate without equivalent customer data scale.
The Forces Accelerating Demand Right Now
Hybrid work infrastructure is the most significant near-term demand accelerator. The shift to distributed workforce architectures — with employees accessing enterprise applications from home networks, hotels, and branch offices — has dissolved the traditional network perimeter that NGFW was designed to protect. Organisations responded initially with VPN-based remote access, which proved inadequate for sustained hybrid work at scale. The permanent solution — SASE combining SD-WAN with cloud-delivered NGFW — is driving a complete refresh of enterprise security infrastructure with an estimated USD 8–12 billion in total spending through 2027 for organisations in the Fortune 2000.
OT and industrial network security is the fastest-growing NGFW deployment segment. Operational technology networks — factory floors, energy grid control systems, water treatment infrastructure — were historically air-gapped from enterprise IT networks. Digital transformation initiatives, remote monitoring, and supply chain integration have progressively connected OT environments to IT infrastructure, creating network security requirements in industrial settings where NGFW deployment was previously non-existent. Fortinet's OT-specific NGFW appliances (FortiGate Rugged series, rated for industrial temperature and humidity ranges) have established early market leadership in a segment growing at 18%–22% annually.
What Is Holding This Market Back
SSL/TLS inspection performance is the persistent technical constraint. Encrypted traffic now exceeds 90% of internet traffic volume — and NGFW must decrypt, inspect, and re-encrypt each packet to perform meaningful application-layer security analysis. This SSL inspection process requires 3–5x the compute resources of standard packet forwarding, creating either performance bottlenecks or the need for significantly over-provisioned hardware. Customers frequently disable SSL inspection to avoid performance degradation, creating security blind spots that render NGFW protection partial. Vendors have addressed this through dedicated TLS offload ASICs (Fortinet's CP9, Palo Alto's CN-series) but the performance gap remains a deployment constraint for high-throughput environments.
Security skills shortage is the demand-side constraint most consistently cited in customer research. NGFW platforms have become sufficiently complex that effective policy management, threat hunting, and incident response require dedicated security operations expertise that 60%–70% of mid-market enterprises do not employ in-house. This drives MSSP adoption but also creates inertia in NGFW procurement decisions — enterprises defer investment when they lack the internal capability to operationalise the technology effectively.
The Investment Case: Bull, Bear, and What Decides It
The bull case is platform consolidation at enterprise scale: organisations standardise on two or three security vendors (versus current average of 13–15 security point solutions) accelerating NGFW refresh cycles and creating multi-product platform revenue that grows at 20%–25% even in years of flat IT budget growth. The enabling condition is AI-driven security operations reducing analyst workload sufficiently to make platform adoption operationally viable for resource-constrained IT teams. Probability: 55%–60%.
The bear case is SASE displacement accelerating beyond current trajectory — organisations leapfrogging NGFW hardware refresh entirely and migrating to cloud-delivered security architectures, reducing hardware NGFW TAM by 25%–35% by 2030. Leading indicator: the proportion of Fortune 500 enterprises citing SASE as their primary security architecture in annual IT spending surveys, currently at 18%–22% and rising approximately 5 percentage points annually.
Where the Next USD Billion Is Being Built
The 3–5 year opportunity is AI-native NGFW that replaces static rule-based policy management with machine learning-driven adaptive policy — automatically adjusting access controls based on observed user behaviour, device posture, and real-time threat intelligence without manual rule updates. This capability reduces the security operations workload that is the primary adoption barrier for under-resourced mid-market enterprises and creates a sticky subscription revenue model tied to continuously updated threat intelligence. Palo Alto's XSOAR and Cortex platform and Fortinet's FortiAI are early implementations; the commercial scale of AI-native security operations will be defined by 2027.
The 5–10 year transformative opportunity is quantum-safe NGFW — network security appliances and platforms implementing post-quantum cryptography (PQC) algorithms standardised by NIST in 2024 (CRYSTALS-Kyber, CRYSTALS-Dilithium). As quantum computing capabilities advance toward cryptographically relevant scales, organisations with long-lived sensitive data — government, financial services, healthcare — must deploy PQC-capable network security infrastructure before their current encryption is retroactively broken. The NGFW vendor that achieves PQC certification from NSA and NIST standards bodies first will capture the US federal government procurement cycle that mandates PQC migration across civilian agencies by 2030.
Market at a Glance
| Parameter | Details |
|---|---|
| Market Size 2025 | Approximately USD 6.9 billion |
| Market Size 2034 | Approximately USD 18.8 billion |
| Market Growth Rate | 11.8%–14.2% CAGR |
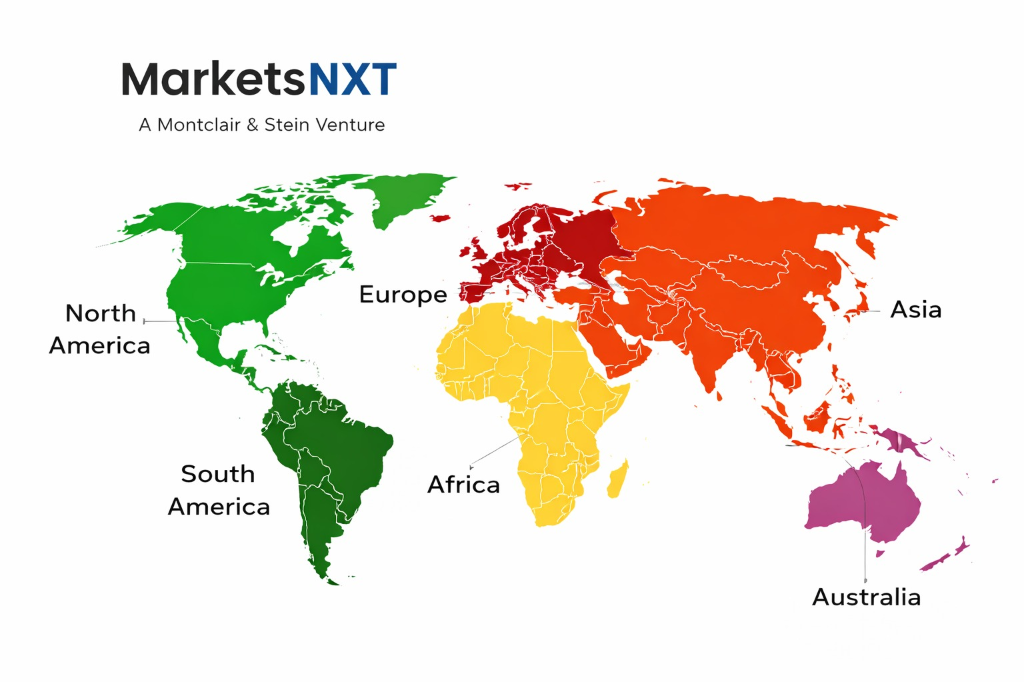
| Largest Market by Region | North America (approximately 44% of revenue) |
| Fastest Growing Region | Asia Pacific (cloud adoption and OT security investment) |
| Segments Covered | Hardware NGFW, Cloud-Delivered NGFW, SASE-Integrated NGFW, OT/Industrial NGFW, Managed NGFW Services |
| Competitive Intensity | Very High — platform consolidation underway; SASE architectural disruption in progress |
Regional Intelligence
North America accounts for approximately 44% of global NGFW revenue, driven by the concentration of enterprise technology buyers, stringent regulatory frameworks (PCI DSS, HIPAA, SOX, SEC cybersecurity rules) creating compliance-driven procurement, and the headquarters of all major NGFW vendors providing a home market advantage in reference customer development. The US federal government's Zero Trust Architecture mandate — requiring agencies to implement identity-verified, continuously monitored network access by 2027 — is creating a USD 3–5 billion government procurement cycle for NGFW and SASE platforms meeting FedRAMP and CMMC compliance requirements. Europe holds approximately 26%, growing at above-average rates as the NIS2 Directive (effective October 2024) creates mandatory cybersecurity investment requirements for approximately 160,000 entities across 18 critical sectors — including NGFW deployment as a baseline security control. Asia Pacific represents approximately 22%, with Japan, South Korea, Australia, and Singapore being the most sophisticated enterprise security markets; China's domestic NGFW market is served primarily by domestic vendors (Huawei, H3C, Sangfor) rather than US-headquartered incumbents.
The Middle East is the fastest-growing regional NGFW market at 16%–20% annually, driven by digital transformation investment from Saudi Vision 2030, UAE Smart Government initiatives, and the concentration of critical infrastructure — energy, aviation, financial services — requiring enterprise-grade network security. Gulf-region sovereign wealth funds' direct investment in cybersecurity infrastructure and the hosting of FIFA 2034 and Expo security requirements are creating concentrated near-term procurement cycles.
Leading Market Participants
- Palo Alto Networks
- Fortinet
- Cisco (Firepower/SecureX)
- Check Point Software Technologies
- Juniper Networks (SRX Series)
- Zscaler (Cloud NGFW/SASE)
- Sophos
- WatchGuard Technologies
- Barracuda Networks
- SonicWall
Frequently Asked Questions
Market Segmentation
- Hardware NGFW Appliances
- Cloud-Delivered and Virtual NGFW
- SASE-Integrated NGFW Services
- Others (OT/Industrial NGFW, Managed NGFW Services)
- Banking, Financial Services, and Insurance
- Government and Defence
- Healthcare and Life Sciences
- Manufacturing and Industrial (OT Security)
- Retail, E-Commerce, and Technology
- Direct Enterprise Sales
- Value-Added Reseller (VAR) and System Integrator Channel
- Managed Security Service Provider (MSSP) Channel
- Cloud Marketplace (AWS, Azure, Google Cloud)
- North America
- Europe
- Asia Pacific
- Latin America
- Middle East and Africa
Table of Contents
Research Framework and Methodological Approach
Information
Procurement
Information
Analysis
Market Formulation
& Validation
Overview of Our Research Process
MarketsNXT follows a structured, multi-stage research framework designed to ensure accuracy, reliability, and strategic relevance of every published study. Our methodology integrates globally accepted research standards with industry best practices in data collection, modeling, verification, and insight generation.
1. Data Acquisition Strategy
Robust data collection is the foundation of our analytical process. MarketsNXT employs a layered sourcing model.
- Company annual reports & SEC filings
- Industry association publications
- Technical journals & white papers
- Government databases (World Bank, OECD)
- Paid commercial databases
- KOL Interviews (CEOs, Marketing Heads)
- Surveys with industry participants
- Distributor & supplier discussions
- End-user feedback loops
- Questionnaires for gap analysis
Analytical Modeling and Insight Development
After collection, datasets are processed and interpreted using multiple analytical techniques to identify baseline market values, demand patterns, growth drivers, constraints, and opportunity clusters.
2. Market Estimation Techniques
MarketsNXT applies multiple estimation pathways to strengthen forecast accuracy.
Bottom-up Approach
Aggregating granular demand data from country level to derive global figures.
Top-down Approach
Breaking down the parent industry market to identify the target serviceable market.
Supply Chain Anchored Forecasting
MarketsNXT integrates value chain intelligence into its forecasting structure to ensure commercial realism and operational alignment.
Supply-Side Evaluation
Revenue and capacity estimates are developed through company financial reviews, product portfolio mapping, benchmarking of competitive positioning, and commercialization tracking.
3. Market Engineering & Validation
Market engineering involves the triangulation of data from multiple sources to minimize errors.
Extensive gathering of raw data.
Statistical regression & trend analysis.
Cross-verification with experts.
Publication of market study.
Client-Centric Research Delivery
MarketsNXT positions research delivery as a collaborative engagement rather than a static information transfer. Analysts work with clients to clarify objectives, interpret findings, and connect insights to strategic decisions.